
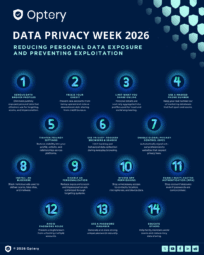
Data Privacy Week 2026: Reducing Personal Data Exposure and Preventing Exploitation
It’s Data Privacy Week 2026. To mark the occasion, we’re sharing some tips to help you stay more private and better protect yourself from the dangers of personal data exploitation. Whether it takes the form of phishing, smishing, vishing, password cracking, impersonation, identity fraud, Account Takeover (ATO), or Business Email Compromise (BEC), the weaponization of personalContinue reading "Data Privacy Week 2026: Reducing Personal Data Exposure and Preventing Exploitation"





